A Momentary Lapse of Reason: An Appeal to the Hack-Savvy
My wife has just watched a big chunk of her life disappear: every e-mail or Gchat she ever sent or received since 2007.
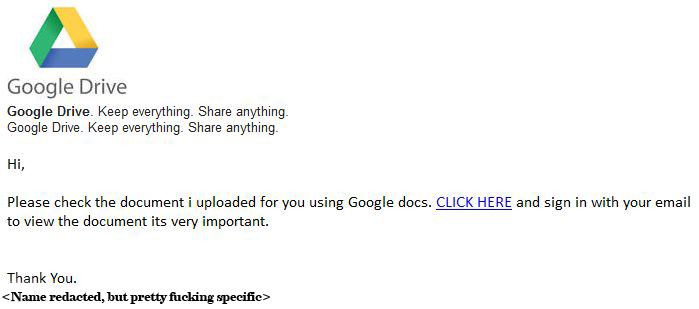
This is how it began:
In a moment of dumbness, Caitlin clicked on the link: believe it or not, given the specific context of the missive it was actually plausible that it came from the person whose name was attached. Ever since then, everyone on Caitlin’s contact list has been getting the same message (some of us twice), this time signed “Caitlin”. And this is a savvy hack indeed: those suspicious enough to actually write back, asking if this was legit (the e-mail certainly lacked anything even close to the BUG’s narrative voice) received another e-mail in response, assuring them in the same fractured English that yes indeed, Caitlin was the actual author. At the same time the little fucker deletes your Gmail contact list; unless you have a photographic memory or an offsite record of your contacts, you lose the ability to send a mass warning to those on the hit list. The most you can do is wait until various perplexed and angry people write back, one by one, and reply to them in turn.
Clever, then, but obvious phishery; I Googled a bit and learned that those who get suckered by this scam find themselves on a faux-Google page that tries to trick them into entering their Gmail login credentials. I also discovered that this agent doesn’t limit itself to e-mails; it’s starting to infiltrate blogs and impersonate actual posts (although even less convincingly in that context).
Here’s the thing, though. While I’ve seen this fucker in action, and while I’ve found alerts at malware monitoring sites and on Google forums, I haven’t found a single reference to its ability to wipe out the entire contents of one’s Gmail account. And that does seem to be the kind of thing that would warrant some sort of mention.
Caitlin lost tens of thousands of cloud-borne e-mails. She never bothered to make local backups, trusting Google’s servers for such security— and while Google does apparently offer archiving services for paying customers, the most they do for us freeloaders is recommend that we keep local backups. (We will save for another time my rant about why you should never trust your data to the fucking cloud, and why certain authors who smugly proclaim “We are not going to retreat from the cloud” either have their heads up their asses or are taking kickbacks from Google. Does anyone think the Cylons would have been able to pull it off if everyone on the Twelve Colonies had been running Xp?)
Things have improved between this paragraph and the last. One of the BUG’s IT-savvy friends has come down to our booth (we’re drowning our sorrows at the Duke of Somerset) and discovered that her MacBook Air has, in fact, retained a scrambled and intermittent local backup of sorts. All is not lost, only some; and while the date-stamps on the remainder are totally fucked, the text of the surviving emails seems to be intact.
Still. That was a fortuitous happenstance on a local flash drive. The definitive archive in the cloud is just gone — and from what we can tell, the surviving local subset will get nuked the moment we connect with that cloud. Something up there is still lurking in Caitlin’s account, hungry for kibbles and bits; it’s the Ebola of computer viruses, so virulent that it’s bound to implode from its own lethality before it has a chance to conquer the world.
It’s conquered the BUG’s account, though. And the weird thing is, nobody else who’s reported this phish seems to have experienced anything remotely close to that level of lethality.
I know you people, as a statistical population if not as individual faces. A lot of you eat bytes for breakfast.
Any suggestions?




Your pizza boxes make wonderful toys to turn on others, methinks.
Sounds like a mutant strain, it seems to happen with alarming frequency these days.
Does she have a mobile phone connected to her Google account? If so, turn of the syncing feature right bloody now, and then check to see if she has her contacts and email archived on it.
She can then create a new Gmail account, and re-sync to the new one. Or just save her contact list out using any number of apps, depending on what kind of phone she has.
Have you both reviewed all the settings on https://www.google.com/settings/security for your google accounts, and have you turned on two-step verification? Check “Connected applications and sites” on that page. Review what’s in there so you know what you’ve given permissions to that uses your google credentials. If you’re not sure what it is, revoke it.
Once you have 2-step authentication, if someone has your password on another machine, they will also need to have your phone or backup phone to be able to log in.
One more piece of information is required from you. If Caitlin did in fact get taken to the redirect fake site and actually entered her login information, it’s quite plausible to think that someone harvested that data and used it to drive a script to remove e-mail at those sites. Gmail could stop that by requiring success at a live-human “captcha” screen, but either they don’t do that, or it was in fact a human using purloined data, possibly going down a list of phished accounts and trying for maximum damage of anyone who seemed the least interesting or important. “Script Kiddies” are generally evil little creatures who lend credence to the people who like to trot out that saying about “one trait shared almost universally in Asperger’s is a nearly devout cheerful malice”.
I don’t want to be too specific with suggestions here, on the chance that it’s actually personal to y’all rather than just mindless computer malice… if I gave you a suggestion and you implemented it as suggested, and it only made things worse as well as wasting time and effort, I would feel really bad.
Alternatives? Well, you guys could run a linux/*BSD box at home and convince it to do POP type transactions with at least one swerver out in the Amazon Cloud. A little tricky for newbies but there are HOWTO docs out there, or just see the docs that come with code off of SourceForge.
The idea with this would be that you’d have all of your correspondence on a hard-to-hit (and maybe as hard to use, for non-*NIX people) machine at home, but you’d have most of your mail transactions taking place out in Teh Cloud with automated backup to mirror servers also out there. Amazon Cloud has pricing structures that for your need probably would amount to “free or nearly free”.
You could also just set up a pretty basic Amazon Cloud mail server and just pull that via SSH/SSL POP3, where the mail would be collected at and sent from that server, getting downloaded to your laptop/workstation mail browser every so often. Set it up the right way, and you might need considerable bandwidth in case of image/movie/music files, but the full mail spool could be retained both in the cloud and on your respective browsers. I think that would be some variations on IMAPD and POP3, somewhere along the line you might need to pay up for an SSL certificate, or just rely on SSH passphrase authentication. I used to do something like this for my mother’s mail, causing mass confusion when migrating through major version upgrades in Netscape Full Version, Thunderbird, etc. But data was only ever duplicated, never lost. There must be actual hundreds of clients and server-add-on freewares for these modes. If you want to cause huge trainwrecks and get barraged with disinformation, try going to slashdot.com and ask “even though I prefer Sendmail, I’m considering alternatives.” I predict this will spawn at least 30 subthreads about whether or not to trust self-certified TLS even in the DMZ with side trips into k3w1 h4x with Pyzor. (At least 50 subthreads will question your sanity for even considering Sendmail. It’s big and ungainly but a hard target when done right. There are smaller lighter faster more popular apps handling mail in most places nowadays.)
If you ever decide you have far too much time and need to consume far too much caffeine and analgesics while battling a hellish learning curve, go with Sendmail, SpamAssassin and all pre-requisites including all of the Pyzor stuff, procmail of course should be the local delivery agent for the server shell accounts, then set up some TLS (“transport layer security”) POP3 web-based access so your browser can exchange mail with the server. Sendmail can be made fairly bulletproof, and if you go with an Amazon Cloud server based solution, just install one of the basic Ubuntu 12 images, get logged in, and from the command-line do `apt-get update; apt-get upgrade ; apt-get install sendmail spamassassin pyzor procmail` and say “Y” to the bewilderingly long list of things it wants you to install as prerequisites. Provisioning a world-routable IP address from there via their easy-but-confusing web interface is left as an exercise for the student, as is modifying your DNS records to turn the resulting WMD into mail.rifters.com for example.
This sounds insanely complex but there are HOWTO docs out there that will walk you into owning a pretty secure and generally low-spam cloud mail server of your own. Mirror it to backup and you are set “for life”.
Or just get another gmail account but put a post-it note on the monitor that says “gmail: here be tygers” and never ever do anything by reflex. As the saying goes, “for you are crunchy, and good with ketchup”. Probably the best solution, all around.
What a day, anyways figured out a way to restore Caitlin’s gmail using the backup. I just tested it on mine (feeling a bit like Norman Osborne or the “Green Goblin”) with bits of back up I made while we were at dukes.
Internet, you scary!
You’re definitely not alone in this. The Atlantic ran a big piece of pretty much the same scam, thanks in part that the victim was one of their correspondents’ wife:
http://www.theatlantic.com/magazine/archive/2011/11/hacked/308673/
Similar thing happened to a guy from wired:
https://academized.com/blog/apple-amazon-hacking
These are the higher profile hacks that have gotten media attention and as a result Google has taken steps to restore their data.
There are a lot of cases like these which don’t get the same amount of attention though:
http://productforums.google.com/forum/#!topic/gmail/W6o2cWEkhVo
Good luck taking back control over your addresses and make sure to change all of your passwords afterwards and use 2 factor auth wherever possible.
Google has a built-in backup for contacts that works for unpaid accounts as well (on the webpage: Contacts->More->Restore Contacts, here’s a photo-guide: http://www.wikihow.com/Restore-Google-Contacts) that I’ve used before. Despite what they tell you, they also have backups (but not for long) of your emails, so try reaching out to them, because you might be able to restore the data. As Hristo Erinin writes, mention the rogue hack and possibly the large network presence that both of you have.
And a general note: for the love of all that is holy, enable two factor authentication (SMS + password) for your Google account if you do care about it’s contents. It doesn’t help for all attacks, but it would stop this one (because each “client” application gets a unique password, so this worm would not be able to log on with BUGs normal one).
I didn’t mention all the stuff Non Entity said up there because I wasn’t sure how much work you want to do… but since Non brought up a lot of what I was thinking…
POP/IMAP
I’ve enabled IMAP on my gmail accounts. It’s not too difficult and you can enable POP/IMAP to use with email clients. The gmail docs walk through how to configure clients to do this.
Redundant email services
You could have gmail forward all of your messages to a remote service. Or visa versa. I have a pobox address that forwards to different mail services for me, including gmail. Not everyone uses my pobox address, but I am aware of that and make informed choices about making redundant copies.
Storage in general
For files in general — I have been using DropBox and SpiderOak (similar to dropbox). DropBox is fairly easy to use. SpiderOak less so, but they also focus on zero knowledge policy about the data they are storing for you. You can run these on multiple machines, including your remote server.
Web hygiene
extensions — On firefox, get extensions like httpseverywhere and noscript. They can be fairly fucking annoying sometimes because a lot of sites don’t work without going through and deciding what to give permissions to, and I don’t always know why someone is using javascript from another service. Similar things exist on Chrome.
clicking — when hovering over a link see if it is spelled correctly, is using weird unicode character sets, has a lot of javascript cruft on it, etc. A lot of times though, I even don’t bother clicking things in email and I go and type in the url by hand.
Password hygiene
Password safes are handy. You can generate passwords that you don’t know and then pull out the password safe so you can use copy/paste. This means you need to have a nice master password.
Email hygiene
Email addresses are almost like passwords these days, because of how they get used for password recovery. You could go so far as to use non-obvious emails for some services. You could pick ljkdfdkh@example.com for the email that you associate with a service you are using.
Emails that purport to come from the service desk
When I worked at a corp, the service desk would send legit warnings about phishing spam that managed to get inside the company, and would also get people to change their passwords. But there are also phishing mails that look like these kinds of messages. Sometimes I’d just call the service desk to see if they actually sent the message before following the instructions.
I forgot to mention using ssh tunnels. On the mac there is a friendly app called SideStep that will help you through the process of setting up an ssh tunnel when it detects that you are on an open wireless connection.
This is a really fun talk by Jessica McKellar where she talks about the internet. and at some point, gets to open wifi and how to sniff packets (wireshark). then talks about an exploit where someone could intercept traffic and redirect it to a page of happiness rather than the target page.
http://pyvideo.org/video/1677/how-the-internet-works
t=1068s starts talking about wireshark.
t=1200s encrypted channels, irc not encrypted. sniff password, django4life, woo
t=1297s how to propose marriage using scapy and ARP-cache poisoning
Hristo Erinin,
Also use 2 factor auth with other services. facebook, dropbox, etc.
OMFG “Registered Sex Etc” now these are a fracking annoyance!
This is another example of “never do things by reflex”. Was watching the film “Savages” tonight and in one scene is a poster at a hax0r lab: “Social Engineering. Because there is no software patch for human stupidity”. Note that the URL for the name takes you to a site that seems legitimate in showing you maps of convicted sex offenders… but are they phishing? Doing cross-site javascript attacks? Just trying to get folks to sign you up for scams? Or, more worrisome, did this get past moderation by someone who has phished the password for this site? In which case apologies for the “never do things by reflex”.
@Shiela: Thx for the many suggestions which were much more clear than I was. Folks, her suggestions are all pretty darn good, specifically IMAP and then especially that bit about packet-sniffing with Wireshark. See also AirCrack NG. AirCrack can power through pretty much any “standard” WiFi encryption; SSH is pretty much a bare minimum if you want to pretend to any safety using WiFi. SSL is even not all that secure, as the key-lengths in use can be brute-force cracked pretty quickly by a decent high-school computer lab if they have the right software. Of course, SSH with 1024-bit key length can be a little slow for some uses but just fine for mail.
I should add that `alpine`, a text-only mail (and usenet heh) browser which evolved from `pine`, has a nifty feature where the links are highlighted, and in brackets following is the FQDN (machine name) of the actual link as opposed to the text label of the HREF statement. If the highlighted link says “www.youronlinebank.com” and the bracketed text reads [znarfax.h4x0rvi113.com] that’s a pretty obvious indicator. For what it’s worth, I’ve been gotten by the tw1tter.com scam. Rather embarrassing.
Ah this is not good. But anyway, and I didn’t scan all the comments to look if someone had already commented on this, a while ago Google had a bug in their system and hundreds of thousands of people lost their Gmail and GDocs data to that.
Google was able to restore everything. Because, get this, they have TAPE backups. Serious fucking tape, that no one but them seems to use anymore. Maybe you can inquire about that, because I’m almost sure they haven’t changed their policy there.
Sorry to hear about this though, I hope things will work out eventually.
If you want a local copy that stays yours…
Use POP not IMAP – with IMAP, deletions can cascade. I watched as a friend decided to get rid of her local copies of an organisation’s emails (she resigned as chair, and was passing the address on to the next person), and the cloud copy lost all its emails from her term.
Buy/assemble desktop (franken?) PC, install Kubuntu (easier for Windows refugees to pick up) and Thunderbird, get Thunderbird talking POP to your gmail account -> local copy of all your emails from that point.
Think of it as linux without pain.
Mr Non-Entity,
I’ve been thinking of using alpine. Mail.app is annoying, and I don’t remember Thunderbird being that great. Everyone keeps fucking around with their webmail interfaces. I think I was pretty happy when I used pine. (I’m not badass enough to use mutt).
I think I might switch to using alpine in screen.
How to back up all your gmail emails to another gmail account (using POP):
http://www.guidingtech.com/5299/backup-gmail-using-another-gmail-account/
Mr Non-Entity,
Oh and I want to say — you had a lot of the same stuff there, but I was worried it sounded daunting and wanted to try and write it up slightly more approachable (if possible). If people are interested enough, then maybe at one of the sf cons in the area someone should have a party room that is actually a room for helping people understand all this stuff. There are cryptoparties, so why not something more basic like — things you can do that you might have thought were too complicated but aren’t really.
@Sheila: Now there’s the seeds of an awesome idea!
@Peter Watts: Maybe you can help promote this! I mean, the notion that various Cons might want to have Security Clinics. After all, SF readers and writers might reasonably be presumed to be technophiles. My own observation is that most are in fact technophiles, and in the most interesting way: while being frequently quite technically adept within their own specialty, they are often pretty adept outside of that specialty. While most might not be techies or IT folks, most have managed to become “power users” or adepts at the workaday tech such as browser or mail-handler usage, page and site creation, etc., to say nothing of generating content. 😉
There are, however, some folks out there who love a good hard-SF story and who are hardcore IT gurus. A lot of these attend Cons and you might be surprised to discover the backgrounds of some of the Filkster types. They might not be living in the stories they love to read, but day-to-day they are elbow deep in the fluidities that gush anywhere in the vicinity of the Leading Edge (or “bleeding edge”). This is where you find 50+ year guys dressed as Ewoks (but not as Pedobear!) and singing hilarious songs and if anyone inquires, they’re all named John. Or Bob. Ask them what they do In Real Life and they’ll tell you “networking” or “server admin” and possibly most of them are really saying “can’t talk much about it”. I bet there are a fair number of them who wouldn’t mind taking a few hours out of the revelry to help a group of their favorite writers muddle through the mind-numbing basics of header-munging and packet mangling. Though if I was one of the writers who is a bit timid (perhaps rightly so) of the fans, I don’t know if I’d want my Reverse Writers’ Clinic delivered by a bunch of guys dressed up as Boba Fett or Imperial Storm Troopers. Maybe they could dress up as Tux instead.
Really, it might not be a bad idea. Imagine someone going to a Con and trying to force-pair with the iPads of various staff & presenters, only to run afoul of a network full of a lot of newbie anti-intrusion hobbyist SF writers overseen and assisted by Sincerely Evil Bastard sysadmins who had thought this was their long-deserved vacation…
I really need to stop posting story ideas here. Though maybe I show up at some Con and hand out demo discs of US patent 7,464,403. <evil grin>
Hello Mr. Watts.
I’m still wondering what you could say about the questions that I asked you earlier. about Aliens in the way of your book. You asked me for references to scientific work on the subject and I gave them to you. Unfortunately,
the control system of your blog post does not allow hyperlinks, so I gave you the names to search for on Google. I am especially interested in this topic, because I have a suspicion of participation in a conspiracy of some writers,
propagating false information about Aliens.
This is easy to fix. If email is something you care about, perhaps it makes sense to pay an email provider that has a policy on restoring accidentally/maliciously deleted email and supports a variety of two-factor login methods.
I don’t get kickbacks from fastmail.fm, nor am I an employee; I just think it’s more sensible for people whose bread and butter is writing to outsource server administration and configuration to Morlocks such as myself.
I would recommend that your wife get her own domain for email, if she hasn’t already; it’s a layer of indirection that makes it a lot easier to switch your mail from one service to another, if the need ever arises.
michiel,
Oh hey, I use fastmail as my secondary mail provider. I’ve had an account there since before gmail (iirc). I keep them because of the philosophy of “if the service is free then you are the product” type of thing with google.
pobox -> fastmail and various other addresses
Mr Non-Entity,
I sort of thought that is what a cryptoparty would be like — with a friendly track for novices but I floated the idea with someone who was planning a cryptoparty in my neck of the woods and he didn’t think it was in the spirit of the party they were throwing so I dropped it and decided one day to gather like minded people to do what I had imagined.
There is actually a longer story to this involving me going to PyCon Canada and SFContario on the same weekend and seeing a talk about Mozilla Persona at pycon, and seeing a talk about the future of privacy at sfcon. It seemed to me that everyone should get together and discuss it from a user perspective with tips and tricks. I thought perhaps to suggest it as a panel for the next con, and mentioned it to the guy from Mozilla as an idea — but when you think about it, it would probably be more useful as a little workshop thing — or an ongoing lab room kind of thing where volunteers have hours so someone is always around to help and teach.
I’m going back to Pycon Canada, but this year it is not at the same time as SFConatario so it is less likely that I’ll go to it again. Which is why I haven’t pushed to come up with any materials to propose. I’ve helped run a newbie workshop for python in general… so I think I could help someone with more specialized stuff. would just need about 5 volunteers at any one time maybe? haven’t through through how a lab would work. The beginner workshop was a day with a laptop setup the night before. an open lab would work diff and I’d have to think about it.
For future reference, the app linked below (still in beta) claims to download the GMail directory. Comes in Apple, Windows, Linux flavors. Think I’ll be using it at some point. Horror stories tend to make us be more careful. My empathy to Caitlin regarding what I hope will only be a temporary problem.
http://gmvault.org
Folks, sometimes it’s a good idea to be “just mildly paranoid” which usually works unless someone really “able” comes after you, and they most likely won’t be doing it with a script and quite likely you won’t even know they’ve been there. The “mildly paranoid” consists of things like frequent data dumps of things such as mail inbox and outbox and address-book, and if you can automate that, do so in a way that’s a revision-control system. Don’t over-write previous records or you could be over-writing useful information with a whole lot of “1” or some-such. Do it more like “mail-out-date1, mail-out-date2” etc[1]. I don’t know if gmail will let you do periodic XML dumps in the same way you can dump Blogger content, but if it will, do that fairly frequently. Just be advised that a fairly capacious notebook external drive might be a good investment if you’re going to do this, and also be advised that you are much better off to archive to CD-ROM than to DVD-ROM; the capacity difference is far offset by the greater durability of the CDs.
@Shiela: My take on the crypto folks — and I come from back in the day before Phil Zimmerman had to hole up in a trailer park in Arvada hiding from the Feds — is that they can get a bit too paranoid even for me. Entire volumes, many of them, are left unspoken in that final phrase. For those of us such as myself who are only mildly out of our minds (living anywhere near DC, it’s a given for the best-case) mere GPG or PGP from the old *BSD source is probably quite enough. Encrypting your laptop’s screen is not quite as bad as doing that and locking your keyboard into a mode of chord twiddling on the function keys so as to decrypt enough to get to a login prompt, pulling out even the BIOS battery, and locking the unit into a Faraday cage and only then declaring it “possibly almost safe”. I have met such people. I have almost been such people.
For every one who doesn’t want to go down that road, just tell yourself “somewhere there is probably someone who is more evil than I am paranoid,” do backups, and if the horse gets out of the barn, as the saying goes, you’ll know how to lock the stable doors better in the future. BTW, pogoplug with archlinux is a pretty portable and low-power local backup solution if you’re not needing an onboard RTC/bios clock, and you can buy one (less mass storage) for around U$45 or so.
Regards,
Ref:
1. If you can figure out a way to incorporate the revision-control and version-history model of MediaWiki, or just cut-and-paste to your own mediawiki instance on a local-only network, that might be just about the ideal solution. Got vandalized? Just revert to the last good version.
Go to https://support.google.com/mail/contact/bugs?ctx=bugflow_receive31 immediately. You have roughly 30 days from when your emails were first deleted to get them back through this process; this can work even if they were “permanently deleted”, but you have to notify Google that your account was compromised. Some emails might be completely gone, but you should get the vast majority back. And turn on 2-factor authentication!
I work at Google, so although I have no connection to the team that manages this, let me know if you’re running into a wall and I’ll see what I can do.
@Michiel
Google does offer 2 factor authentification… and you do not have to pay a cent for it.
I believe it is sensible to have it turned on. It is just a bit of a hassle.
Everyone:
Thank you. Dual authorization enabled; tokens revoked. And I will not stop browbeating the BUG until she has a reliable local backup down here at the Magic Bungalow.
As for myself, while I was not victimized, I have decided that a couple of home external hard drives and the occasional uploaded megazipfile is probably not sufficient, and henceforth will be using Caitlin to shuttle an external hard drive back and forth to the Attorney-General’s office as a kind of off-site storage that doesn’t rely on that fucking loathsome cloud thingy.
Turns out I have a few actual Google employees among the readership. One of them posted in this thread (hi Hugh), a few contacted me offline, all have offered to help get the rest of the BUG’s e-mail back one way or another. I thank you all; I will never have a chance to enact all the various options and safeguards put forth by everyone here, but it’s good to know that those options exist, and how to access them if necessary.
Dark Hanter-X, please stop asking me about my opinion of humanoid aliens. I asked for citations from the peer-reviewed primary lit; until I get them, I gotta lump your claims in with the rest of all that von-Danikenesque fantasy that would be really cool if it were true but, sadly, isn’t. I want to believe — but not that much.
@Peter Watts, who wrote in-part: […] that doesn’t rely on that fucking loathsome cloud thingy.
I interviewed for a few jobs just a few years go, and the most recurrent question was “so what do you think of Teh Cloud”. Most of the interviewers managed to almost keep a straight face. Basically, you could instantiate an awesome Amazon Cloud machine, do incredibly cool and powerful things to and with it, and some guy with a silly haircut can click their mouse in three places and your work is all gone forever.
Don’t want to rely on the cloud? Don’t, then! Here’s one way.
You could try PogoPlug, and use their cloud services, but that is not what I recommend. I recommend taking a look at Pogoplug Devices, specifically the Series 4 unit for about U$40.00. It’s about the size of a pack of cigarettes. You attach really quite a lot of laptop external USB-3.0 drives to it. At least a terabyte or three.
Get the unit, sign up for the free version just to get a device unlocking password, and then install ArchLinux ARM, which is a semi-independently developed Linux with a kernel for the ARMEL 4 processor, a very reliable workhorse. The general code trees and software packages are quite close to the Debian or Ubuntu packages, meaning that they are pretty darn strong in terms of security. The ArchLinux ARM system probably should get a fairly hefty 50 gig partition on the hard-drive, make another partition 32-gig for swap (virtual memory on disk), and split the rest of the drive into two partitions, one for MSDOS and one for Linux. If the drive is a nice 1.5Tbyte laptop external, you can pack quite a bit onto it. It will all fit into a smallish cigar box. No cloud. At this time you would be doing business with ArchLinuxARM.org and they are free software and lots of it.
Pogoplug is losing their ass on their cloud services, but their “plug server” lines are excellent. The Series 4 is 800MHz and for a backup server and file-server for the local network, that is quite adequate. The only drawback is that it needs access to another machine (or network) with Network Time Protocol (NTP) or your timestamps will date you a bit before Apollo 13.
Generically, these are “plug devices” or “plug servers“. There are lots to choose from.
Cheers, and see also Freedom Box article from Wikipedia
“I asked for citations from the peer-reviewed primary lit”. You really think, if our
obscurantist’s science, permit this materials to publication?
I think any journal printing rigorous evidence of extraterrestrial intelligence would instantly become the most popular publication on the planet, and people would fall all over each other for the chance to be associated with such an earth-shattering discovery. Not many would cover up the chance to become a household name worldwide, with a stack of Nobels on their shelf.
But that’s not what this thread is about. Henceforth, let’s stay on-topic.
I hate to play Negative Nancy here, but you know experience…
Had an author friend who ran a message board on a popular free service. The system got hacked systemwide. Years of cool discussions on many topics were lost. Not too long after that they completely redesigned the system. They even renamed/rebranded. To appeal to what I suppose was either a wider audience or the Belieber/Twilight crowd, they also added new capabilities like really large, obnoxious cutesy fucking icons.
For whatever reasons, my author friend decided to run his own messageboard software on his own (rented) server space.
Within days, it got hacked. He had backups but first he had to regain control of his server space, figure out how it got hacked, plug the security holes, and restore it.
He wound up, as I recall, going back to the newer site.
I’m not entirely sure what the moral of the story is. Probably something about trading one set of problems for another combined with there not being many viable even near-perfect solution. Going with eggs in baskets, you’ve got synced in at least three places (cloud, removable drive as backup, and portable device for use when the cloud is unreachable), and really why not hard copies of at least select portions as well?
And if most of that doesn’t happen automatically, you practically need a cut-off portion of your brain to nag you into keeping up with it (yes, I think I crossed two threads with that) or hire a personal assistant.
Roswell!!! Roswell!!!!
This has all been a v interesting read.
The best security might be sprinkling the universe with shards of your life, with both digital/digitized and non-digital info. Smatterings of things on hard drives, flash drives, cellphones, cloud servers, CDNs, notebooks, photo albums (remember THOSE cumbersome things)… and let’s not forget, things spoken/told to others. The only catch is that these facets of your exoself should NOT be linked in any useful or obvious way.
There’ll be a bit of you wherever you go / wherever you log in / jack in. Hmm… like a sort of holographic personal security. Cumbersome for the owner maybe, but hopefully even more cumbersome for haXors…
What a stuff of un-ambiguity and preserveness of valuable familiarity
concerning unexpected emotions.
Did the fine folks who brought/will one day bring us the T-virus merge with Horse eBooks?
> umbrella corporation, on June 2nd, 2013 at 7:46 pm Said:
It’s a botspammer